This post shows step-by-step how to apply RBAC rules to enable metrics displays for an already RBAC-limited user. This is a continuation of this post on how to set up RBAC in Lens This demonstration uses the Lens Desktop Kube (LDK) cluster, and the Lens built-in metrics but should similarly apply to any cluster/prometheus-based metrics configuration.
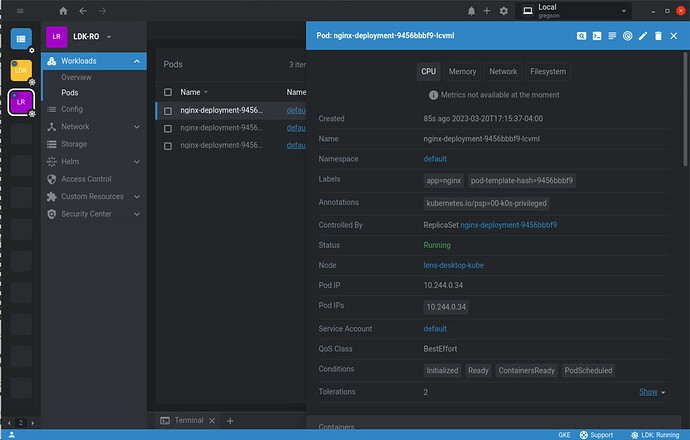
For the developer-reader user (service account) from the previous post, because it is limited to pod read access, the built-in metrics are not available, as seen on the details page for a pod:
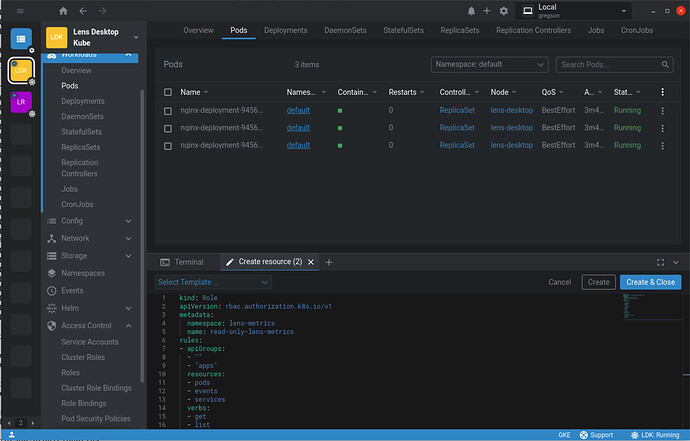
To enable metrics for developer-reader connect to the LDK cluster via the admin user (where there is more than pod read access possible) and create the following Role.
kind: Role
apiVersion: rbac.authorization.k8s.io/v1
metadata:
namespace: lens-metrics
name: read-only-lens-metrics
rules:
- apiGroups:
- ""
- "apps"
resources:
- pods
- events
- services
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- "services/proxy"
verbs:
- create
This role applies only to the lens-metrics namespace and doesn’t impact the access that developer-reader has in the rest of the cluster. As before, this Role resource can be created in Lens:
Finally, a RoleBinding is required to associate this Role with the developer-reader user:
kind: RoleBinding
apiVersion: rbac.authorization.k8s.io/v1
metadata:
annotations:
namespace: lens-metrics
name: read-metrics
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: read-only-lens-metrics
subjects:
- kind: ServiceAccount
name: developer-reader
namespace: default
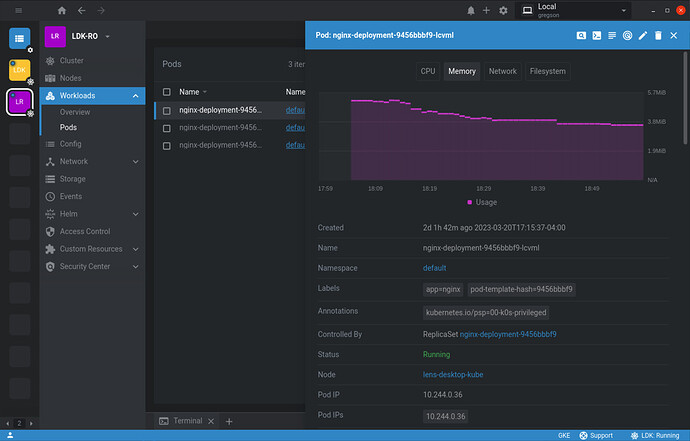
Once it is created in Lens, return to the LDK-RO cluster (which is the developer-reader context). Disconnect and reconnect to ensure that the roles and bindings are picked up, and observe the details page for a pod now includes metrics: